Cyber security is as important for smaller businesses as it is for big name brands. Small businesses are the most vulnerable to attacks because they have less robust protection.
That’s why we decided to make a complete checklist that doesn’t leave a stone untouched in protecting your data. There is a diverse range of services, from a password manager and VPNs to auditing software, this is all your growing business needs to avoid the vast majority of attacks. All you need to begin is to read our quick descriptions to determine what protection your business lacks.
Ajax security system

This product was recommended by Amina Yepisheva from Ajax Systems
Ajax is a smart wireless security system for ultimate protection. It protects the property from break-in, fire, and flooding, as well as deliver home automation. If trouble comes, the system immediately activates the sirens, alerts users via mobile app, and requests help from the alarm response company. The system is engineered to protect both the premises and the site. Motion detectors won’t react to animals. And it’s easy to integrate video surveillance into Ajax.
ExpressVPN

This product was recommended by Gabe Turner from Security.org
VPNs, or Virtual Private Network, as essential for users working remotely or in public spaces like coffee shops. In a nutshell, they encrypt your web traffic and hide your real IP address, which makes you much less susceptible to hacking.
LastPass

This product was recommended by Gabe Turner from Security.org
Password managers not only store all of your passwords in an encrypted vault. They also perform a password audit, seeing which of your passwords are old, weak or repeated. This ensures that you’re not using the same password, or a variation of the same password, for multiple accounts. Many password managers also include two-factor authentication, which sends a passcode to another device, or multi-factor authentication, which has users use fingerprint or facial recognition to access accounts. This ensures that accounts are more protected and that only authorized users are accessing them, ideal for any account that has sensitive customer or company data.
Identity Guard

This product was recommended by Gabe Turner from Security.org
Identity monitoring software monitors your credit and bank accounts for any changes, which may indicate identity theft. This is perfect to use for a business so you can be alerted immediately if there are any new tax returns filed in your business’ name, among other capabilities depending on the service.
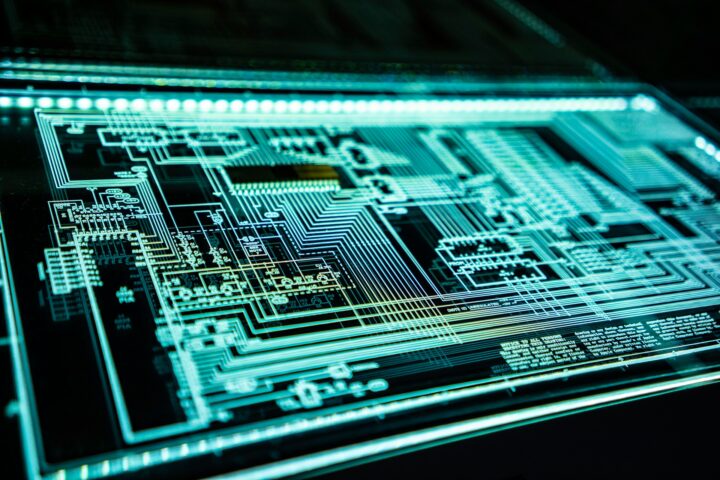
Cytrust

This product was recommended by Debora Lima from Cytrust
Despite the big headlines that name Fortune 500 companies and multinational corporations in costly data breaches, a majority of hacks – roughly 70% of them – target SMEs, with more than half of companies targeted going out of business within six months due to the expenses associated with recuperating data. However, 80 percent of data breaches are entirely avoidable. Cytrust cyberscoring allows small businesses to easily determine their risk exposure to cyber attacks, and helps them obtain best-in-class protection products.
Digital Resolve Multifactor Authentication

This product was recommended by Bill Calpin from Digital Resolve
Now more than ever, with more people working remotely, SMBs are under immense pressure to prevent unauthorized access to sensitive data and personal information. Multifactor authentication is one of the most effective ways to securely manage that access. While the basic concept is simple, the benefits are great. With multiple layers of authentication in place, hackers can be proactively prevented from accessing company accounts, data, networks and systems―even if they have somehow obtained a single password. Digital Resolve’s offering also combines behavioral profiling, device identification and calculated risk factors to automate the authentication process in a transparent yet powerful manner. Should a login attempt be deemed suspect, adaptive authentication options spring into play to provide robust protection that’s hard to bypass-no matter how seasoned the criminal.
1Password

This product was recommended by Mark Soto from Cybericus
Out of all the password managers out there we’ve found this to be the easiest to use and to set up for customers. It’s also one of the few where you can use them for any device. One of our favorite features about it is the Watchtower feature which detects if any of the passwords being used are weak, compromised or reused. The price is great is affordable for just about any business size. For businesses that often have to type in account credentials on different websites or log into the cloud (fake websites are popping up all the time) password management software is a must for companies if they want to maintain high cybersecurity standards.
Netwrix Auditor

This product was recommended by Alexandra Murzina from Netwrix
Netwrix Auditor gives organizations visibility they need to protect sensitive data, ensure business uptime and simplify compliance reporting. Small organizations often rely on manual processes. In case of a security incident, they have to spend a lot of time to crawl through logs to find out what has happened, who had their privileges elevated, when and by whom, who accessed which file and so on. If an organization has to adhere to compliance regulations, they have to make regular reports for the auditors, sometimes in a spreadsheet. Netwrix Auditor automates all these processes, so organizations can receive alerts on malicious activity, investigate incidents in a couple of clicks and get ready for compliance checks much faster. The software is easy to deploy and use, so organizations can have it up and running in a couple of minutes to get the value immediately.
pfSense

This product was recommended by Lumena Mukherjee from SectigoStore
pfSense is an opensource firewall/router solution with an impressive feature set that can rival most commercial software. It can be configured or upgraded using a web-based interface.
Snort

This product was recommended by Lumena Mukherjee from SectigoStore
Snort is a cross-platform, opensource IDS/IPS solution that performs real-time traffic analysis to log and block network events based on configurations.
CodeGuard

This product was recommended by Lumena Mukherjee from SectigoStore
CodeGuard is an automatic database/ website backup solution that stores your backup on a separate third-party cloud platform. In the event of a ransomware attack, your backups remain protected and can be restored quickly to resume normal operations.
Quad9
This product was recommended by Lumena Mukherjee from SectigoStore
Quad9 is a free DNS filtering solution that blocks access to sites where malware or other threats have been detected.
ClamAV

This product was recommended by Lumena Mukherjee from SectigoStore
ClamAV is a cross-platform, opensource antivirus software toolkit that can also be deployed to be used as an email virus scanner on the server-side.